Symantec Proves Russian “Dragonfly” cyber unit responsible for US critical infrastructure hacking

CSA Z462 Arc Flash Training – Electrical Safety Compliance Course
Our customized live online or in‑person group training can be delivered to your staff at your location.
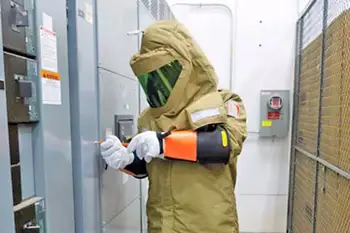
- Live Online
- 6 hours Instructor-led
- Group Training Available
WASHINGTON - An October, 2017 report by researchers at Symantec Corp., cited by the U.S. government, has linked recent US power grid cyber attacks to a group of hackers it had code-named ““Dragonfly cyber unit”, and said it found evidence critical infrastructure facilities in Turkey and Switzerland also had been breached.
The Symantec researchers said an earlier wave of attacks by the same group starting in 2011 was used to gather intelligence on companies and their operational systems. The hackers then used that information for a more advanced wave of attacks targeting industrial control systems that, if disabled, leave millions without power or water.
U.S. intelligence officials have long been concerned about the security of the country’s electrical grid. The recent attacks, striking almost simultaneously at multiple locations, are testing the government’s ability to coordinate an effective response among several private utilities, state and local officials, and industry regulators.
While the core of a nuclear generator is heavily protected, a sudden shutdown of the turbine can trigger safety systems. These safety devices are designed to disperse excess heat while the nuclear reaction is halted, but the safety systems themselves may be vulnerable to attack.
Sign Up for Electricity Forum’s Newsletter
Stay informed with our FREE Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
The operating systems at nuclear plants also tend to be legacy controls built decades ago and don’t have digital control systems that can be exploited by hackers.
“Since at least March 2016, Russian government cyber actors… targeted government entities and multiple U.S. critical infrastructure sectors, including the energy, nuclear, commercial facilities, water, aviation, and critical manufacturing sectors,” according to Thursday’s FBI and Department of Homeland Security report. The report did not say how successful the attacks were or specify the targets, but said that the Russian hackers “targeted small commercial facilities’ networks where they staged malware, conducted spearphishing, and gained remote access into energy sector networks.” At least one target of a string of infrastructure attacks last year was a nuclear power facility in Kansas.
Read The Complete Article Here:
http://online.electricity-today.com/electricity-today/spring-2018/~18/